This article applies to customers who self-host a Netskope One DSPM instance within their own infrastructure.
Overview
These instructions are used to define an AWS CloudFormation template that provisions all AWS resources necessary for running a Netskope One DSPM environment within your own AWS VPC.
Prerequisites
Before beginning, the Netskope One DSPM application AMI needs to be shared with your organization. To request a trial AMI, please contact your CSM and supply:
- Your AWS account number; and
- The AWS region where you will deploy the Netskope One DSPM instance (which we require in order to share the image).
- Ensure you have a SSH key pre-configured in the AWS account where you will deploy the Netskope One DSPM instance. Visit the AWS EC2 console to check if your desired SSH key pair exists, or create one yourself.
Configure CloudFormation Stack
Excerpt: AWS: Configure CloudFormation: Instructions 1
For the account where you will configure the CloudFormation stack, log into the A
- For the account where you will configure the CloudFormation Stack, log into the AWS console. The CloudFormation Stacks dashboard is displayed.
- Select the target region, if necessary.
- On the dashboard, click the Create Stack button and select the “With new resources (standard)“ option. The Step 1 screen is displayed.
- Under the Specify template section, enter the following value in the Amazon S3 URL field:
https://dasera-release.s3.us-west-2.amazonaws.com/CreateDaseraVMFromAMIAndDaseraUser.jsonExcerpt: AWS: Configure CloudFormation: Instructions 2
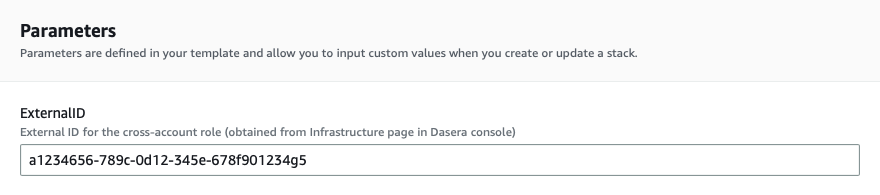
In Step 2, under the Parameters section, enter the following values:
- Click the Next button. The Step 2 screen is displayed.
- Complete the required Name field.
- Under the Parameters section, enter the following values:
| Parameter | Value |
|---|---|
| ExternalID | Enter the like-named value from the previous section above. |
| Parameter | Value |
|---|---|
| AMIImageId | AMI ID of the Netskope One DSPM image shared with your organization. This value can be found in your AMI Catalog in the My AMIs section. Clear all filters and filter by Owner = “Shared With Me”. |
| SSHKey | Name of the SSH key you wish to install on the instance. Installing patches and security updates requires an admin to connect to the instance via SSH. |
| SecurityGroupId | Your own AWS security group that you wish to associate. Please ensure the security group belongs to the same network as the subnet you will launch Netskope One DSPM, otherwise deployment will fail. |
| SubnetId | Subnet to launch the Netskope One DSPM instance into. This will determine the VPC and availability zone of the Netskope One DSPM instance. |
Excerpt: AWS: Configure CloudFormation Stack: Instructions 3
Proceed with configuring the remainder of your CloudFormation deployment as desired. When ready, navigate to the final step, click the Submit button, and monitor the build to completion.
To learn more about the resources created by the above actions, please expand the following section:
Resources Created
On the Resources tab, the following resources are listed:
| Resource Type | Resource Name |
|---|---|
| EC2 Instance (m5.2xlarge) | Netskope One DSPMInstance |
| IAM Role | Netskope One DSPMRole |
| IAM Role | Netskope One DSPMGlueServiceRole |
| IAM User | Netskope One DSPMUser |
Configure CloudFormation Stack: Roles
In addition, the following permissions are assigned to the new IAM Roles: Role N
In addition, the following permissions are assigned to the new IAM Roles:
Role Name: Netskope One DSPMRole
| Permission Name | Purpose |
|---|---|
| AWSGlueConsoleFullAccess | Provides full access to AWS Glue via the AWS Management Console |
| AmazonEC2ReadOnlyAccess | For getting regions and instance IDs |
| AmazonRDSReadOnlyAccess | For discovering RDS clusters |
| AmazonRedshiftReadOnlyAccess | Required for discovering RedShift clusters |
| AmazonAthenaFullAccess | Required for discovering Athena clusters and running scans |
| AmazonS3ReadOnlyAccess | Required for scanning S3 |
| AmazonDynamoDBReadOnlyAccess | Required for scanning DynamoDB |
Role Name: Netskope One DSPMGlueServiceRole
| Permission Name | Purpose |
|---|---|
| AmazonS3ReadOnlyAccess | Required for scanning S3 |
| AWSGlueServiceRole | Required to allow access to related services including EC2, S3, and Cloudwatch Logs |
Generate API Keys
Once your deployment is complete, you will need API keys for later use in connecting Netskope One DSPM to the current AWS Account. Generate a new pair using the following instructions:
Excerpt: AWS: Generate API Keys
Navigate to the IAM Management Console > Users section . The Users list is dis
- Navigate to the IAM Management Console > Users section.
- The Users list is displayed.
- In the User name column, click on the Netskope One DSPM User hyperlink.
- The User Summary screen is displayed.
- Navigate to the Security credentials tab.
- Under the Access Key section, click the Create access key button.
- The Create access key modal is displayed.
- Download or copy the following values to your local machine for later use:
- Access key ID
- Secret access key
Next Steps
- Access your new Netskope One DSPM instance to validate its installation. To learn more, please visit our Accessing Netskope One DSPM on AWS article.
- Connect Netskope One DSPM to your AWS Accounts so Data Store discovery & scanning can begin. To learn more, please visit our Introduction to onboarding AWS Accounts article.